Bluetooth security is essential when designing a connected device.
Today, Bluetooth-enabled devices – ranging from headphones to smartwatches and IoT sensors – are everywhere. But whilst the convenience of these devices continues to grow, cyberattacks exploiting Bluetooth vulnerabilities are also on the rise.
So what level of security can we expect from these connected devices? Let’s explore the current state of affairs and the latest developments in Bluetooth security.
Bluetooth: a brief history
Bluetooth is a short-range wireless technology used to transfer data between devices. Operating on the 2.4 GHz frequency, Bluetooth connectivity is a protocol that involves dividing data into packets and transmitting each packet over one of the 79 Bluetooth channels.
The Bluetooth Special Interest Group (SIG) was established in 1998 to oversee the development, licensing and trademarking of this technology. The SIG, originally comprising five companies – Ericsson, IBM, Nokia, Toshiba and Intel – grew to 400 members by the end of its first year and now has 30,000 member companies.
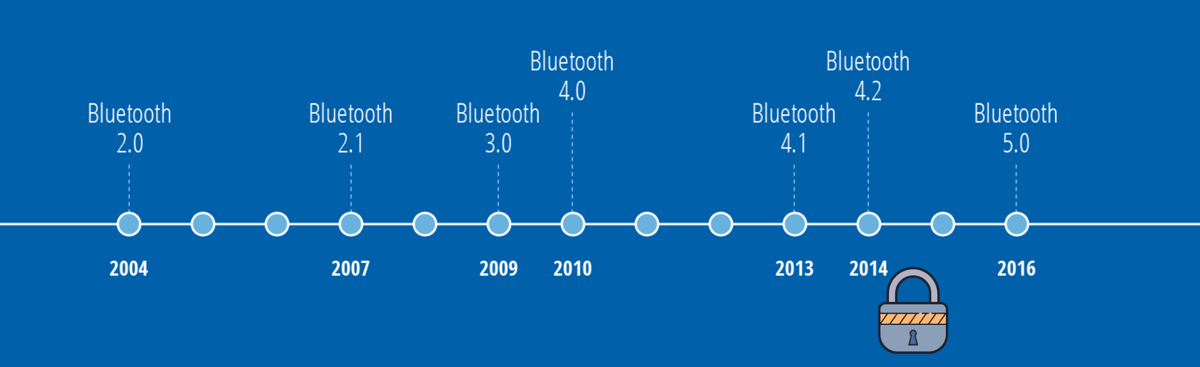
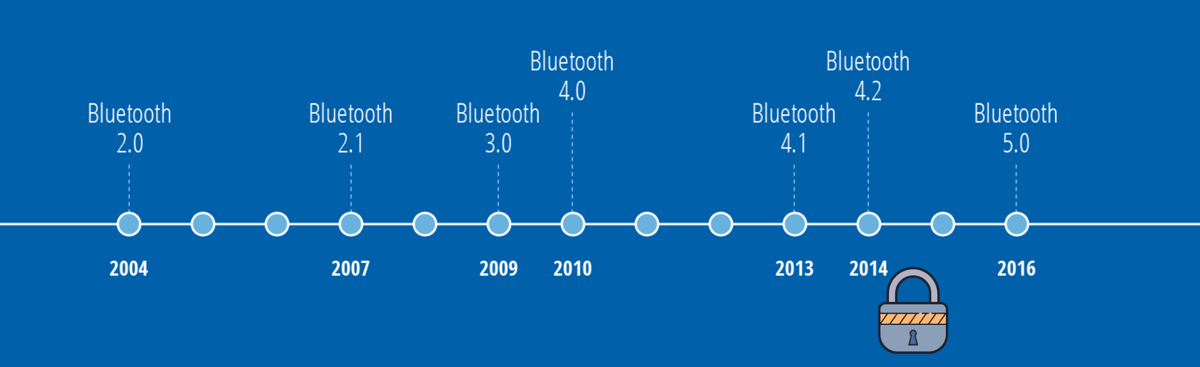
Bluetooth really began to be used with the advent of the first Bluetooth-compatible phone in the 2000s. This was followed by the second major evolution of Bluetooth: version 2.0 + EDR in 2004.
Bluetooth 2.0 + EDR
The most significant feature of version 2.0 was the implementation of Enhanced Data Rate (EDR) technology. This enabled users to theoretically increase data transfer speeds to a maximum of 3 megabits per second (Mbit/s).
Power consumption was also halved compared to the previous version. However, encryption in this version was optional, as was EDR, and could even be disabled!
Bluetooth 2.1
The arrival of Secure Simple Pairing (SSP). As you’ve probably guessed, this is when the concept of pairing with a Bluetooth device first began to emerge. With SSP, mandatory encryption for all connections made ‘man-in-the-middle’ attacks more difficult. These types of attacks involve third parties intercepting and relaying messages between two parties who believe they are communicating directly with each other.
‘Sniff-subrating’ is another important feature of this version. This function was designed to extend the battery life of devices that are inactive most of the time – such as keyboards and headsets – by reducing the active operating cycle of Bluetooth devices.
Finally, the introduction of the Extended Inquiry Response (EIR) improved the filtering of devices that appear during a connection search.
Bluetooth 3.0 + HS
The main feature of this version is its high-speed data transfer. Thanks to 802.11 Wi-Fi, it can achieve data speeds of up to 24 Mbit/s, which is eight times faster than three years ago. It is capable of transferring large amounts of data using the 802.11 connection for faster transmission, whilst using Bluetooth for discovery, connection and configuration.
Bluetooth 4.0
The emergence of Bluetooth Low Energy (BLE) and the first real divergence from traditional Bluetooth. Bluetooth 4.0 – also known as Bluetooth Smart – was primarily designed to transmit data frequently to devices, such as smart devices, whilst conserving energy.
This allows the use of batteries as small as coins, enabling a new way of collecting data from sensors, such as heart rate monitors and thermometers. Companies in the health and fitness sector have taken advantage of this new feature by creating all sorts of devices capable of monitoring and transmitting physical data to a smart device.
In addition to the Bluetooth Low Energy function, this version also introduced the Generic Attribute Profile (GATT), used to provide the device profile, and Security Manager (SM) services with AES encryption.
The design of the chips for Bluetooth 4.0 allowed for two types of implementation: dual mode and single mode. The former is used to create a BLE device, whilst the latter implements the BLE protocol on an existing, conventional Bluetooth controller.
Bluetooth 4.1
This version primarily introduces support for multiple roles and the ability to switch communication channels automatically.
Bluetooth 4.2
This version of Bluetooth was introduced in 2014 by the Bluetooth SIG to eliminate range limitations once and for all by enabling devices to use Internet Protocol version 6 (IPv6) for direct access to the internet. This means that sensors and smart devices can transmit data directly over the internet.
Another advantage of this version is the increase in speed and privacy. Bluetooth 4.2 has increased the technology’s data packet capacity by around tenfold, making it 2.5 times faster than the previous version. The security features of this Bluetooth version have made it more difficult to track your device without authorisation.
This is the first iteration where the security features are starting to be acceptable. Today, it is unthinkable to develop a product without using version 4.2 as a minimum. And yet, there are still many devices that do not use this version, including some smartphones that are not compatible.
Bluetooth 5.0
This version offers improvements to Bluetooth in terms of range, speed and data transfer capacity.
Bluetooth 5.1
This is a rather hardware-based innovation this time, as it adds the ability to determine the direction of radio signals. To do this, the receiver or transmitter will need to be equipped with an array of antennas. This will enable the receiver to determine the angle at which the signal was sent or received, and thus the direction in which the transmitter is located, so that it can indicate this to the user. This is valuable information to help, for example, locate an object using a smartphone, as Bluetooth currently only allows the latter to indicate approximately how far away the former is.
Bluetooth 5.2
Version 5.2 focused on improving energy efficiency with the introduction of LE Audio, enabling audio transmission over BLE. This paved the way for devices such as low-power hearing aids.
Furthermore, the Enhanced Attribute Protocol (EATT) improved data transmission by enabling multiple simultaneous connections, offering a better user experience in complex environments.
Bluetooth 5.3
Bluetooth 5.3 has enhanced security with advanced verification mechanisms to reduce the risk of man-in-the-middle attacks. It has also introduced improvements to reduce latency and manage bandwidth more effectively, which is particularly useful in congested environments.
Bluetooth 5.4
Designed for the IoT, this version introduced support for Public Broadcast Keys, enhancing security and flexibility in large-scale networks. It also optimised protocols for ultra-low-power devices, such as industrial sensors.
Bluetooth 5.5
Bluetooth 5.5, although still in the roll-out phase, promises significant improvements, including increased range and enhanced security thanks to the integration of advanced encryption protocols. It could also introduce connectivity features that are interoperable with emerging standards, thereby consolidating its role within the IoT ecosystem.
Bluetooth Mesh Security
Bluetooth Mesh is establishing itself as an essential standard for IoT sensor networks. This technology adds layers of encryption and authentication at the network and transport levels. By 2024, Bluetooth Mesh-based solutions will effectively prevent eavesdropping attacks through the use of dynamic session keys.
To find out more about Bluetooth Mesh, we recommend this article.
The different levels of Bluetooth security
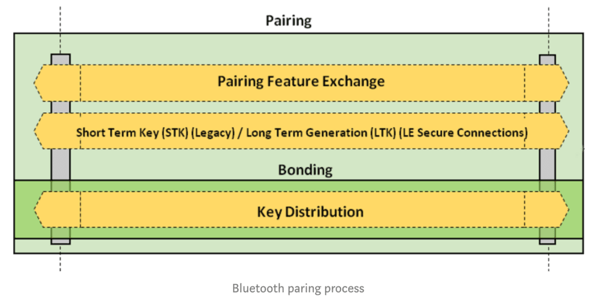
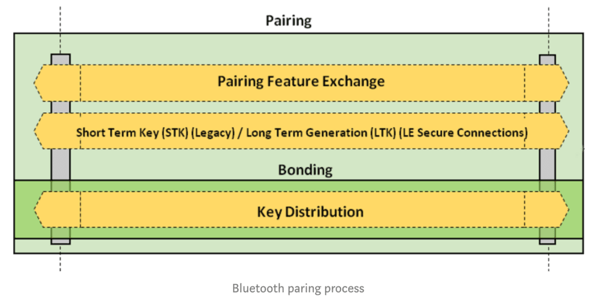
We will see that there are different ways to establish a secure connection using Bluetooth. To initiate this connection, the request always comes from a master device. In BLE, there are two types of devices: the master (your smartphone, for example) and the slave (the object you wish to connect to, such as a speaker). When a central device attempts to access a characteristic of a protected peripheral, a pairing request is sent. Pairing is the basic mechanism of Bluetooth which, through various methods (which we will discuss later), enables the exchange of keys between the central device and the peripheral, thereby establishing a secure connection.
Pairing involves authenticating the identity of two devices, encrypting the connection using a short-term key (STK), and then distributing long-term keys (LTK) used for encryption. The LTK can be saved for faster reconnection in the future; this is known as ‘bonding’.
As you will have realised, the security level of your device depends entirely on the method used to establish this key exchange. However, not all available methods are equal, and they depend on your device’s capabilities. Let’s look at what these methods are and how to choose the best option for your device.
For a BLE connection, the Generic Access Protocol (GAP) defines two security modes, as well as several security levels per mode. These modes are as follows:
Mode 1 (encryption and authentication)
Enhanced security by adding a layer of encryption and authentication.
- Level 1: No authentication or encryption required. This level should obviously be avoided, as it offers no security for your device.
- Level 2: Encrypted communication (AES-CMAC), but no device authentication.
- Level 3: Encrypted communication (AES-CMAC) and object authentication.
- Level 4: Encrypted communication (using the ECDH method and BLE 4.2) and object authentication.
Mode 2 (data signing)
This mode adds a data signature during communication between devices.
- Level 1: Signed data without authentication. Suitable for non-sensitive IoT sensors.
- Level 2: Signed and authenticated data. Essential for critical devices such as medical devices.
Mixed mode
The object can handle both signed and unsigned data.
Available pairing modes
The pairing process is where all security-related decisions are made. Its purpose is to determine the capabilities of each device preparing to pair, and then to enable them to actually communicate with one another. The pairing process takes place in three stages, which we will briefly describe.
Phase 1:
In the first phase, the two devices inform each other of their capabilities. The values they exchange are those of the Assignment Protocol (ATT). These values operate at Layer 4 of the Logical Link Control and Adaptation Protocol (L2CAP) and are generally never encrypted. They determine the pairing method to be used in phase 2, as well as what the devices can do and what they support. It is therefore the device’s hardware characteristics that will define the level of security possible during the exchange.
Phase 2 :
In the second phase, the aim is to generate a short-term key (STK). To do this, the devices agree on a temporary key (Temporary Key) combined with random numbers, which gives them the STK. The STK is never transmitted between the devices. When an STK is used, this is referred to as LE legacy pairing. However, if you wish to use ‘Secure Connection Only’ mode, a long-term key (LTK) must be generated at this stage (instead of an STK), and this is known as LE Secure Connections.
Phase 3:
In phase three, the key from phase two is used to distribute the remaining keys required for communication. If an LTK key was not generated during phase two, a key is generated during phase three. Data such as the Connection Signature Resolution Key (CSRK) for data signing and the Identity Resolution Key (IRK) for generating and retrieving private MAC addresses are generated during this phase.
There are four different pairing methods:
- Numeric Comparison: This method involves both devices displaying the same six-digit value on their respective screens or LCD displays. It is then up to the user to ensure they match. This allows the devices to be identified relative to one another.
- Just Works: It is obvious that not all devices have a screen, such as headphones or a speaker. Consequently, the Just Works method is probably the most popular. Technically, it is the same as Numeric Comparison, but the six-digit value is set to zero. Whilst Numeric Comparison requires on-the-fly calculations if you attempt a MITM (Man-in-the-middle) attack, there is no MITM protection with Just Works.
- Passkey Entry: With passkey entry, a six-digit value is displayed on one device, and this is entered into the other device.
- Out Of Band (OOB): The principle behind this method is to use a communication channel other than Bluetooth to transmit the keys. The best-known example is NFC. There are other methods based on light. Rtone has also developed an innovative and secure technology for pairing a Bluetooth device. More information at: kiwink.io. In 2024, this method has benefited from innovations, such as the use of light sensors to transmit the keys, making pairing even more secure.
Recent developments have introduced additional options to enhance security and simplify the user experience:
- Secure connections with numeric comparison:
- Available for several versions now, this method is continually being optimised. It relies on a visual check of the displayed keys and uses improved algorithms in version 5.3 and above for greater accuracy and security.
- QR Code-Based Pairing:
- Introduced with Bluetooth 5.4, this pairing mode is specifically designed for IoT devices. By scanning a unique QR code, the user can quickly establish a secure connection, even for devices without a screen or buttons.
These advancements allow users to choose the most suitable method based on the usage context, the device’s hardware capabilities, and security requirements. For example, for industrial or medical use, approaches such as LE Secure Connections or Out Of Band remain essential to ensure optimal data protection.
But then, how do I determine the most appropriate security level for my item?
In short, the security level of your device depends first and foremost on the version of Bluetooth you are using. As we have seen, not all versions of Bluetooth are created equal. This version is, of course, determined by the hardware. Many low-cost phones still have radio processors based on older versions of Bluetooth, which means they cannot establish connections with devices under secure conditions.
Today, it is recommended to use at least Bluetooth version 5.0, which offers modern features and advanced security mechanisms. However, for those still limited to earlier versions, version 4.2 Secure, with ECDH-based encryption, remains the minimum solution to consider to ensure an acceptable level of security.
Next, it is of course the peripherals available on your device that will determine the applicable security level. If your device has no screen, no buttons, no LEDs… You can immediately see that the possibilities for key exchange are limited. In this case, solutions such as Out-of-Band (OOB) pairing, via NFC or QR code, become necessary to ensure a secure connection.
Key criteria to consider
- Bluetooth version: Always opt for a version of Bluetooth 5.0 or higher, which offers better range, faster speeds, and advanced security features such as direction detection (5.1) or BLE audio (5.2).
- Device capabilities: If your device lacks a screen or buttons, it is crucial to provide suitable pairing methods, such as QR codes or OOB systems.
- Usage context: For a product intended for professional or medical use, “Secure Connection Only” mode is essential to comply with security standards and protect sensitive data.
Best practices
- Security by Design: Build Bluetooth security into your product right from the earliest stages of design. This ensures that the very structure of your device promotes data protection.
- Software updates: Ensure that your devices’ firmware supports the latest versions of the Bluetooth protocol and is regularly updated to address any vulnerabilities.
- Testing and Audits: Conduct regular security audits to identify and rectify potential vulnerabilities before they are exploited. This includes testing encryption, pairing methods, and the performance of security keys.
To conclude on this subject
Please be aware that there is no one-size-fits-all solution for ensuring the security of connected devices, as each product has its own specific characteristics and requirements. However, it is essential to bear in mind that the security of your device depends primarily on your choice of hardware and the pairing methods you choose to implement. These are all crucial factors that require careful consideration and, often, specialist support.
Furthermore, Bluetooth Mesh now offers advanced capabilities for securing communications between devices. By introducing encryption and authentication mechanisms at the network and transport layers, it ensures enhanced security, particularly suited to complex IoT environments.
Drawing on our expertise in the design of connected devices, we are here to support and guide you in developing secure, innovative solutions tailored to your needs. So, let’s stay in touch!