Bluetooth MESH, standardised by the Bluetooth SIG in July 2017, has revolutionised mesh networks by providing robust, flexible and secure connectivity for connected devices. Since then, chip manufacturers such as Nordic Semiconductor, Silicon Labs and Texas Instruments have developed suitable implementations and SDKs.
In 2023 and 2024, major updates have strengthened this protocol, confirming its central role in the fields of the connected home, industry and Smart Cities. Discover how these advances are transforming the IoT.
We tell you more in this article.
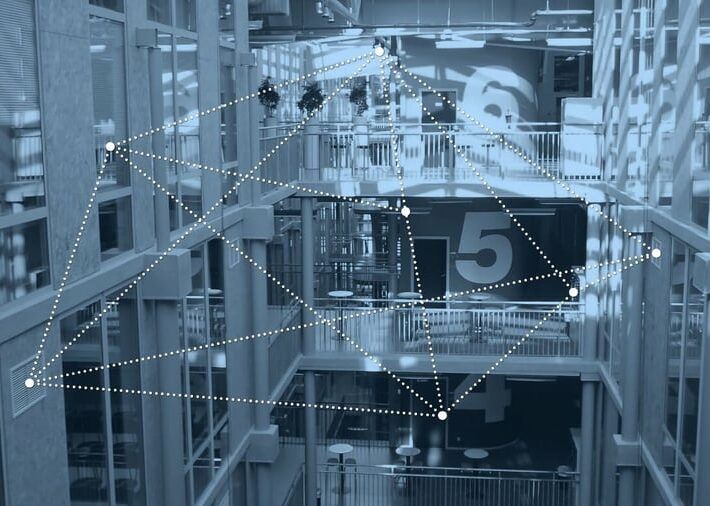
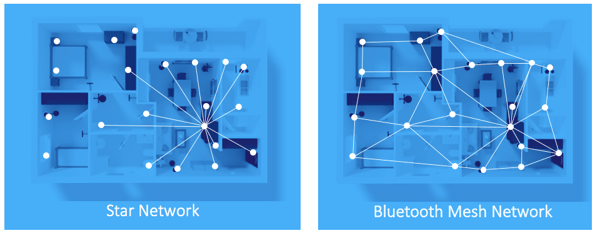
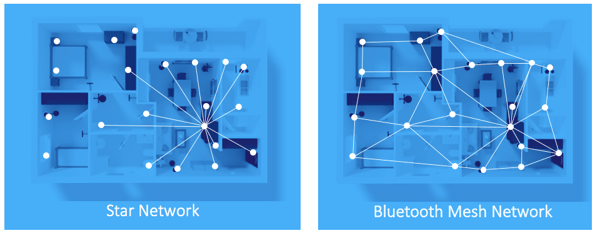
A rich and flexible network topology
Unlike traditional Bluetooth Low Energy (BLE), which requires a star topology, Bluetooth MESH introduces a mesh network architecture. This topology enables:
- The interconnection of a large number of devices (up to several hundred in some cases).
- Extended range through multiple hops, essential for covering large areas.
Ideal for applications such as smart homes or industrial environments, this topology revolutionises the way IoT devices communicate.
In 2023, new features such as remote provisioning and OTA (Over-the-Air) firmware updates were incorporated into the Bluetooth MESH standard. These additions simplify network management and reduce the need for physical intervention, making the technology ideal for large-scale infrastructures such as smart buildings and Smart Cities.
Broadcast Protocol: Managed Flooding
The Bluetooth MESH specification is based on a flooding technique known as Managed Flooding, in which messages are relayed from node to node until they reach all destinations. This approach ensures:
- Increased resilience, as there is no single point of failure.
- Better scalability for networks comprising hundreds of nodes.
In 2024, Bluetooth 6.0 introduced improvements in energy efficiency and latency, further optimising the performance of Bluetooth MESH-based networks.
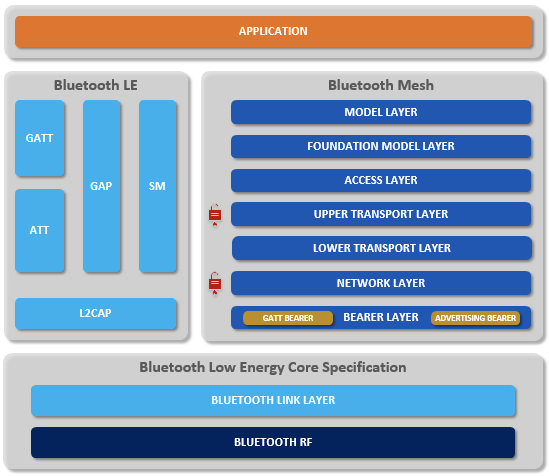
Protocol Stack Architecture: A Comparison with BLE
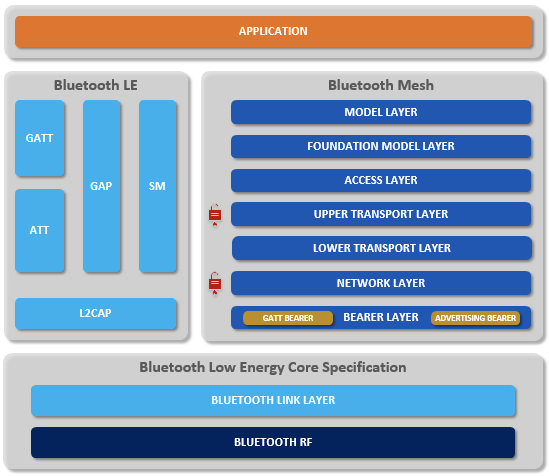
Compatibility with ‘standard’ BLE
‘Standard’ BLE devices that use GATT and are currently in use are not capable of sending Bluetooth MESH messages, nor are they capable of interpreting them.
Bluetooth SIG has therefore provided backward compatibility by incorporating GATT functionality into Bluetooth MESH nodes, enabling connectivity with any device that supports GATT, provided the device is compatible with Bluetooth 4.0 or later.
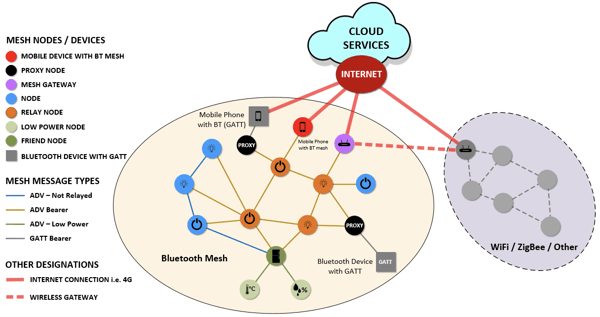
Different Types of Knots
In addition to their ability to send and receive messages, Bluetooth MESH introduces various additional Features that can be combined on each node:
- Relay: receive and relay messages,
- Proxy: receive and relay MESH messages between ‘standard’ BLE devices (GATT) and MESH devices (Publish/Subscribe),
- Low Power: for devices with limited energy resources. They can only receive and send messages to nodes with the Friend feature,
- Friend: enables the reception and relaying of messages to Low Power nodes.
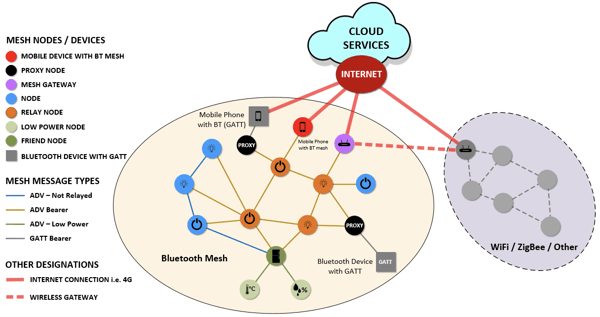
The topology and different types of nodes in a Bluetooth MESH network
Network settings: Resources
The nodes are configured with 4 Resources that define a Bluetooth MESH network and allow users to join it:
- Address: network addresses are required to identify the sources and destinations of messages,
- NetKey: the network key is used to secure and authenticate messages at the network layer,
- AppKey: application keys are used for similar purposes but at the application layer,
- IV Index: this index corresponds to the Time To Live (TTL) used to extend or limit the network’s lifetime.
Network keys and application keys are generated using a random number generator, as defined in the Bluetooth specification. These two keys are shared amongst all nodes across the entire network for the NetKey, or amongst a subset to be isolated for the AppKey.
Communication is only possible if it is carried out using the appropriate network key.
Publication/Abonnement
Devices on a Bluetooth MESH network can send information to multiple devices on the network. The term used for this is Publish. Devices can also be configured to monitor information from one or more sources or from a Group. This is called Subscribe.
A feature called Periodic Publish allows messages to be sent at regular intervals.
Example: in the case of a house with a kitchen containing 1 switch and 2 lights. Each light must be controlled by this switch. In this case, the switch publishes its status to the topic “kitchen” and each of the lights subscribes to this topic. Every room in the house is managed in the same way. A light can also subscribe to multiple topics.
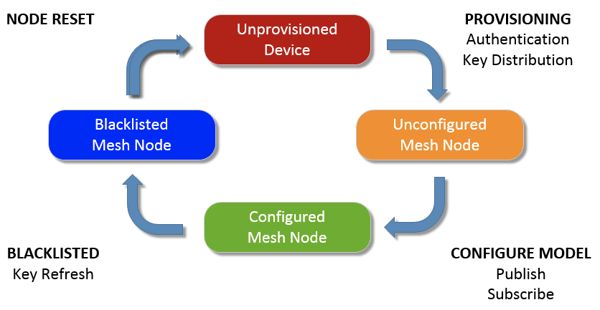
Provisioning
Devices that are not yet part of a Bluetooth MESH network are referred to as unprovisioned devices. These devices broadcast their presence and can be added to the MESH to become network nodes through a process known as Provisioning.
During provisioning, the provisioner, which is usually a smartphone, provides the node with the NetKey, the current IV Index and a unicast address for each element of the node.
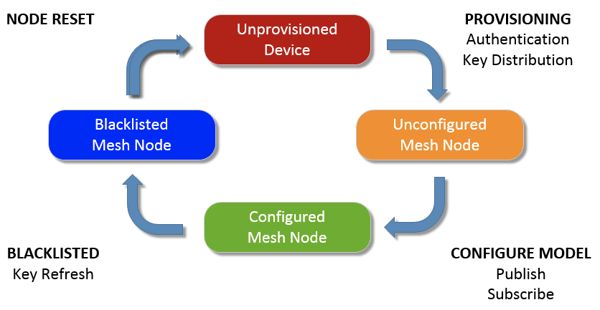
The provisioning cycle for Bluetooth MESH devices
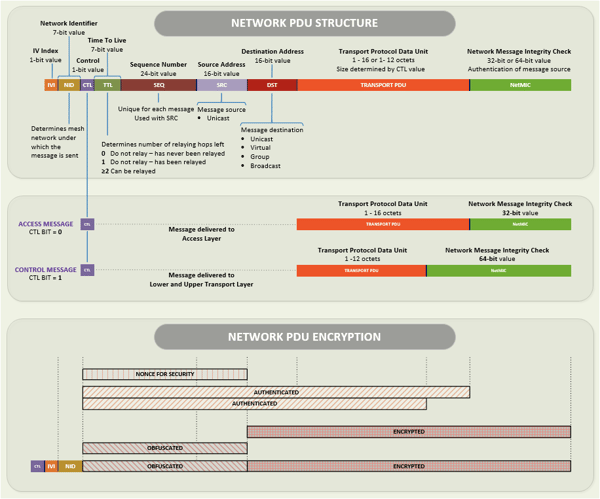
Message Format
All communication within a Bluetooth MESH network is based on the transmission of messages.
The transport layer of the protocol handles message fragmentation when the maximum payload size is reached. Furthermore, messages may or may not require an acknowledgement.
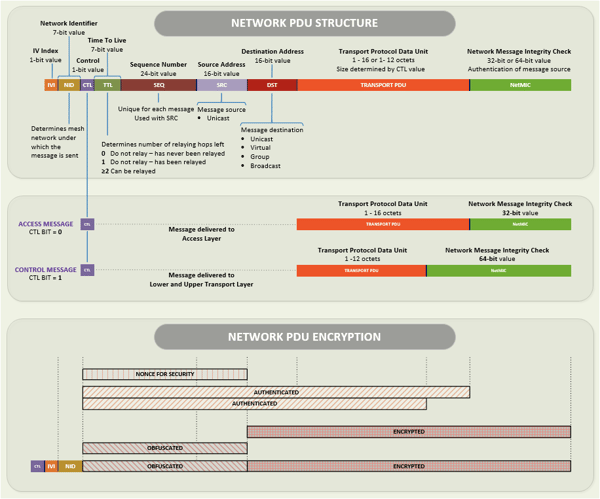
The Bluetooth MESH packet format (PDU)
Addressing
A wide range of IoT use cases require the user to be able to control a single node, a group of nodes, or all nodes simultaneously. This functionality is provided in Bluetooth MESH using Unicast, Virtual and Group addressing
Group addresses are also used for multicasting and can represent multiple elements within one or more nodes.
It is important to note that Bluetooth MESH allows for flexible grouping of all types of devices.
Security
The Bluetooth SIG has always placed security at the heart of its specifications, and Bluetooth MESH is no exception:
- Mandatory encryption and authentication across all layers (network and application).
- Use of AES-128-CCM keys to protect data.
In 2024, encryption of network PDUs was strengthened to include a dynamic nonce model, offering better resistance to replay attacks.
To find out more,
>> Lire l’article “quel niveau de sécurité bluetooth pour mon objet connecté”.
DevKey
The device key is used to authenticate and encrypt communications between the Provisioner and a node. Other nodes have no way of interpreting the communication between these two devices.
The DevKey is the most critical key in the mesh network.
NetKey
The flexibility of the mesh network stems from the fact that any node can be configured to use either a single network or several networks simultaneously. This allows one or more subnetworks to be used by defining subnetwork NetKeys. Subnetworks are groups of nodes capable of communicating with one another at the network layer.
Alternatively, a node may belong to two or more completely separate mesh networks. A good example of such a scenario would be a mobile phone that could be part of a home mesh network, an office Bluetooth MESH network and a vehicle Bluetooth MESH network.
The maximum number of different network keys in an installation is 4096, which allows for the creation of compartments within a network where required.
The NetKey is used to derive other keys using the AES-CMAC cryptographic hash.
AppKey
A mesh network may contain one or more application domains, each with a unique AppKey. Nodes configured with a specific AppKey can receive and transmit messages related to that application, whilst also relaying messages from nodes belonging to different application domains. This enables application isolation, thereby enhancing security.
Network PDU encryption
The only unencrypted parts of the Bluetooth MESH PDU are the VI Index and the network identifier (NID). The rest of the PDU is encrypted using AES-CCM. This makes it impossible to passively eavesdrop on the network structure, as the header, TTL, sequence number, source, etc. are not transmitted in clear text.
Nonces are generated from sequence numbers and other network headers.
Message integrity is protected by a 32- or 64-bit MIC.
The message has a unique 24-bit sequence number. Protection against replay attacks is ensured by using a sequence number that nodes track based on the source address.
Use Cases: Rapidly Growing Applications
Smart Cities
With remote provisioning and OTA updates, the management of connected infrastructure, such as street lighting, becomes more efficient and cost-effective.
Industry 4.0
The reduced latency offered by Bluetooth 6.0 (2024) is ideal for automated systems and industrial environments requiring real-time communication.
Precise Location
Bluetooth Channel Sounding, introduced with Bluetooth 6.0, enables precise device tracking. This opens up new possibilities for logistics tracking and inventory management.
Smart Home
Thanks to the publish/subscribe architecture, managing home devices is made easier. For example, a light switch can publish its status to a topic that several lamps subscribe to in order to synchronise their behaviour.
Conclusion et Références
Bluetooth MESH, enhanced by developments in 2023 and 2024, remains a cornerstone of mesh networks. Its ability to connect numerous devices, combined with regular updates, makes it an essential solution for the smart home, Industry 4.0 and Smart City sectors.
Do you have an IoT project? Contact us to find out how to integrate the latest Bluetooth MESH advancements into your solutions.
- “Bluetooth® Mesh Networking: An Introduction for Developers”, Martin Woolley, Sarah Schmidt, Bluetooth SIG.
- “Mesh Model Specification 1.0”, 2017, Bluetooth SIG.
- “Mesh Peripheral Properties 1.0”, 2017, Bluetooth SIG.
- Adomnicai et al. (2018). Hardware Security Threats Against Bluetooth Mesh Networks, 2018 IEEE Conference on Communications and Network Security.
- Baert, J. Rossey, A. Shahid, and J. Hoebeke, “The Bluetooth Mesh Standard: An Overview and Experimental Evaluation,” Sensors, vol. 18, no. 8, p. 2409, Jul. 2018.
- Murillo, B., Reynders, A., Chiumento, and S. Pollin, “A Multiprotocol Low-Cost Automated Testbed for BLE Mesh,” IEEE Communications Magazine, vol. 57, no. 3, pp. 76–83, Mar. 2019.